Tech firm in Trump dossier was target of antipiracy advocatesBY KEVIN G. HALL
khall@mcclatchydc.comNOVEMBER 15, 2017 12:12 PM
UPDATED NOVEMBER 17, 2017 07:43 AM
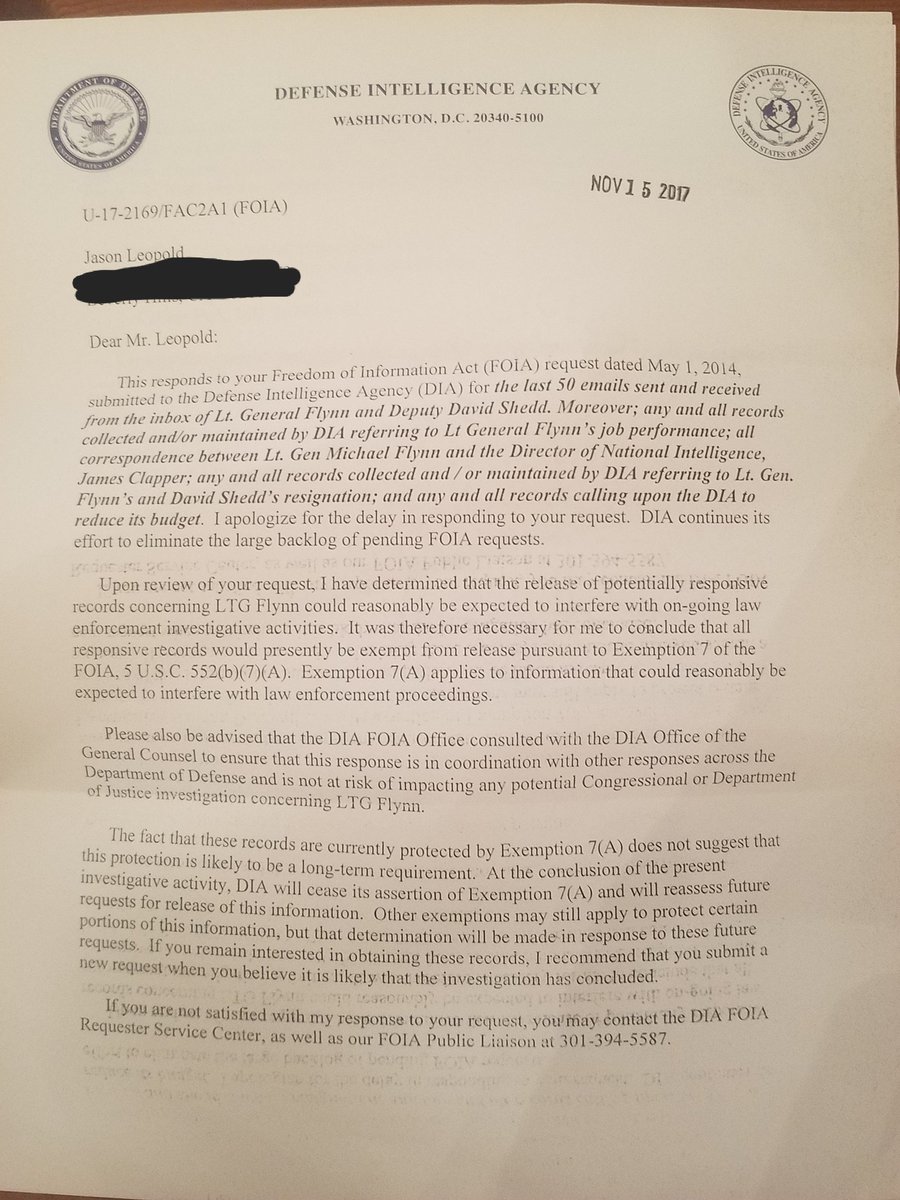
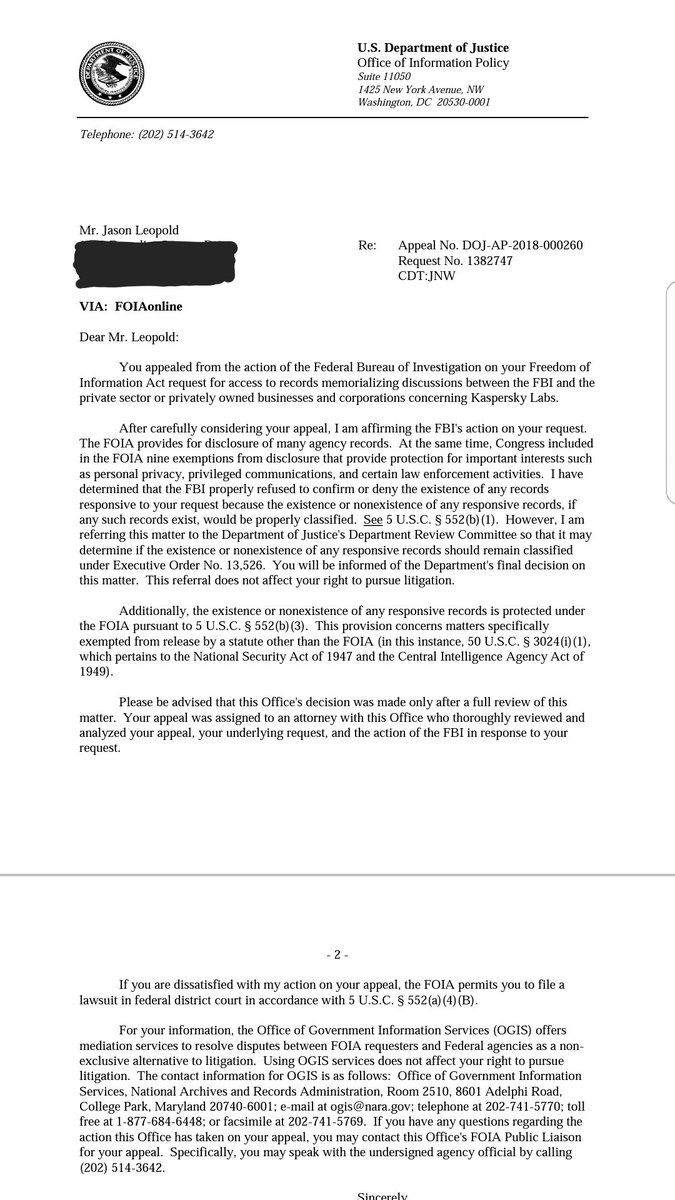
WASHINGTON The dossier that has fueled investigations into Russian connections to Donald Trump’s team got a lot right. Indeed, congressional probes and the first guilty plea in Special Counsel Robert Mueller’s investigation have shown the document’s suggestions that the Kremlin sought for years to cultivate Trump, that it cozied up to key Trump campaign officials, that it worked to sow division in the U.S. electorate and that the campaign had contacts with Wikileaks have all been on target.
Yet among the 35-page dossier’s claims stands one – on the very last page – that is still vexing investigators. It’s the accusation that a company called XBT and its U.S. subsidiary Webzilla hacked the emails of Democratic Party leaders.
“[O]ver the period March-September 2016 a company called XBT/Webzilla and its affiliates had been using botnets and porn traffic to transmit viruses, plant bugs, steal data and conduct ‘altering operations’” against them, according to the dossier, which was prepared by a former British spy who specialized in Russia.
XBT and web-hosting company Webzilla, while not well known to the American public, have long been the targets of lawyers who fight Internet piracy. They have claimed, in several lawsuits and submissions to regulators, that Webzilla looks the other way while its customers flagrantly steal copyrighted materials.
Never miss a local story.
Sign up today for unlimited digital access to our website, apps, the digital newspaper and more.
SUBSCRIBE NOW
None of the lawsuits involve the very specific actions described in the dossier, which was published by Buzzfeed on Jan. 10; XBT has brought defamation suits against the online news site and the document’s author, Christopher Steele, a former MI6 agent.
McClatchy consulted a wide range of experts and reviewed more than 1,000 pages of court documents, U.S. Copyright Office filings and corporate registry documents in Cyprus, Singapore, Florida and the United Kingdom to learn more about XBT. That review yields a profile of a company and, specifically, two corporate employees whose legal entanglements underscore just how difficult it will be for investigators to dismiss the dossier’s claims.
Indeed, Webzilla employees were linked through litigation and regulatory filings to two companies accused of large-scale copyright violations involving Hollywood movies and subscription pornography. Pirated pornography is often baited with malware that can affect users’ computers in various ways.
“It’s not shocking that Webzilla was listed as a hub for questionable activity. Webzilla is on my radar weekly due to its client base facilitating online piracy on a massive scale,” said Jason Tucker, president of Battleship Stance, a company that manages and investigates copyright infringement for film studios.
Unraveling a Mystery
XBT is based in Luxembourg but run out of Cyprus, and has seven subsidiaries, including Webzilla.
Among the allegations against Webzilla: The International Intellectual Property Association, in a Feb. 9 letter this year to the Office of the U.S. Trade Representative, complained that Webzilla, as an Internet Service Provider, “serviced and administered” in Cyprus a company called 4shared.com. That’s a file-sharing website that the trade association said draws more requests to remove specific website addresses from search engines than any other in the world. Gurvits insisted that XBT and its subsidiaries had no control of nor access to the website or its data.
Similarly, in joint comments to the U.S. Copyright Office in 2015, 18 music-industry associations complained that Webzilla and an unrelated company routinely fail to take down copyrighted content “despite receiving thousands of notices of infringement.”
XBT counters these complaints are misguided, saying Webzilla hosts websites much like AT&T offers customers its telephone network but has no control over the content of calls.
“The short answer to it is we have no duty to know,” Valentin Gurvits, XBT’s attorney, with the Boston Legal Group, said in an interview. He added that “100 percent, across the board, I have successfully defended Webzilla against these allegations.”
XBT and its main shareholder have repeatedly offered to open logbooks and take questions from the FBI or U.S. law enforcement but nobody has taken them up on the offer, Gurvits said Thursday. He also branded as frivolous the past lawsuits against XBT and Webzilla.
Still, Webzilla has been involved, even if indirectly, with the kinds of alleged bad actors whose companies could easily carry out the activities the dossier claims.
For example, one Webzilla employee, Constantin Luchian, is linked through legal documents to freakshare.com, which bills itself as a free data-hosting service. Freakshare allows users to upload any amount of data; a download link can then be shared with anyone anywhere.
German newspapers cite allegations from prosecutors that freakshare.com is actually one of several related companies that together make up a global criminal enterprise run by two brothers, naturalized German citizens Kastriot and Kreshnik Selimi.
The two had been sought since 2014 by German authorities for allegedly operating piracy portals where users could watch copyrighted movies for free. Kreshnik was arrested in Kosovo in July, a German newspaper reported on Sept. 11; the Germany Embassy in Washington declined to comment on the case.
Luchian, a Moldova-born naturalized U.S. citizen and an officer in Webzilla’s Florida operations, figures in because he was designated to receive notices demanding that freakshare.com remove copyrighted material from its site. Luchian performs that service for a number of similar firms, which he offers through a business he runs called InCorporate Now. As a result, his name has surfaced in numerous piracy complaints.
Making matters even murkier, the filing designating Luchian to receive notices of copyright violations for freakshare.com was made by yet another company, Vollend Plus LP — a firm with a Scottish address that was registered as trading in batteries and battery parts. Vollend’s paperwork also listed two general partners, both offshore companies in the Seychelles, a known tax haven in the Indian Ocean that requires few details about corporate ownership.
“Vollend Plus is a small Webzilla hosting client but otherwise has no relationship to XBT,” said Gurvits, who actually filed the paperwork for Vollend Plus with the U.S. Copyright Office but said he’s done no other business with it.
Luchian is identified in several other lawsuits alleging theft by companies whose copyrighted materials were hosted by Webzilla or for whom Luchian was identified as the person receiving takedown requests.
“Luchian is a smart guy and he sees an opportunity to provide services,” said Gurvits, who filed the paperwork for freakshare.com and represents Webzilla in its lawsuit against Buzzfeed. He noted that knowledge of Russian is an asset as a registered agent for these companies.
screencapture-incorporatenow-webpage
This screenshot shows Constantin Luchian on the website of his Florida-based corporate services company InCorporate Now. It receives takedown notices for numerous Internet sites when they receive complaints of copyright violations.
Several of XBT’s holdings list an address in Fort Lauderdale at a 24-story corporate office tower. The listed phone numbers are actually for the office-leasing firm Regus. A woman answering the phone said Webzilla doesn’t actually have a suite there. It has a “virtual office,” essentially a mail drop.
XBT’s main shareholder, Aleksej Gubarev, has dual citizenship in Russia and Lithuania, his attorney says. Gubarev has said he resides in Cyprus.
XBT is privately held, meaning it reports very little public information about its owners or its earnings. Gubarev is the controlling shareholder in XBT, said Gurvits, and other employees are minority shareholders.
But corporate registry documents in Cyprus, translated from Greek, paint a more complex structure. They show that over the past seven years XBT’s shareholders have included one entity that appears to have no Internet presence at all, and four that are registered in Singapore or Cyprus. One of the four lists Gubarev as its owner. The others disclose little information about their true owners or directors.
The dossier claims that Gubarev was “recruited under duress” by Russian intelligence officials in the hack of Democratic Party leaders — a charge he vehemently denied in a Jan. 11 interview with McClatchy; Gubarev later filed his suit against BuzzFeed.
Connecting Dots
Cyber experts who analyzed the hack of the Democratic National Committee believe it was the result of a large-scale phishing operation conducted by a group linked to Russian intelligence and a past hack on the Joint Chiefs of Staff.
Phishing involves fake emails sent to email accounts in a bid to have users change their passwords; Russian spy agencies capture them to access private computer networks.
One reason XBT and Gubarev may have drawn suspicion is that their success in the open United States and European markets led to an expansion into Russia last year.
The XBT subsidiary Servers.com opened its Russian operation initially with 500 servers in Moscow, where the Internet is tightly controlled by the Kremlin’s intelligence and military services. Since 2016, Russia has required that Internet providers there store data on servers there, giving Russia both a grip on information and the ability to thwart investigations elsewhere.
“Within Russia, there are increasingly stringent laws governing connecting to the Internet,” said Kenneth Geers, a former NATO cyber expert and fellow at the policy think thank the Atlantic Council. “That’s indicative of a higher level of information control that stems from tighter political control.
An exhaustive review of U.S. court documents by McClatchy found no evidence that XBT or its affiliates were ever accused of spreading viruses or employing robot-like computer commands called bots .
But the piracy lawsuits involving personnel from XBT’s U.S. operations underscore how Webzilla as a hosting company could be used to that end.
A high-profile case in 2013 brought by Disney Enterprises and four movie studios for the Internet theft of copyrighted content ended in a settlement, with the defendant, file-uploading site Hotfile, ceasing its operations.
Luchian and another Webzilla employee —Konstantin Bolotin, a Kazakh immigrant and former Webzilla executive who lives in Hollywood, Fla. — figured in the case because of their email exchanges and business relations with Hotfile’s alleged owner Anton Titov. As recently as this March, Luchian was still the agent in Florida for another Titov firm, Lemuria Communications Inc.
screencapture-hotfile-luchian
This screenshot shows Constantin Luchin as the registered agent to receive takedown notices for Hotfile, a company that ceased operating in a settlement with the motion-picture industry over Internet piracy.
Gurvits insisted that Webzilla’s relationship with Hotfile was limited. “Webzilla did NOT rent servers to Hotfile or give access [to the servers] – only floor space, electricity and Internet connectivity,” he said in an email.
Bolotin and Luchian provided sworn depositions in January 2016 in another case, this one brought by the foreign owner of the Metart Network. Metart operates self-described high-end, members-only erotic adult entertainment websites.
The defendant was Sun Social Media, which, Bolotin said in his deposition, he’d launched after leaving Webzilla. Luchian handled accounting for the new outfit, an adult-themed video-hosting company. Hosted by Webzilla, Sun Social had been sued for alleged theft of Metart’s copyrighted pornographic material.
Sun Social Media didn’t have any employees in Florida, Bolotin testified, just paid programmers in Russia and Ukraine to build and maintain a video-hosting platform for subscription porn at his proprietary websites.
But Bolotin and Luchian had curiously faulty memories in their depositions, each unable to remember under oath the year they graduated high school or college. At the time of deposition in 2016 they were respectively aged 29 and 30.
A Star is Porn
The dossier’s most specific allegation against XBT is that porn was a vehicle through which the viruses and bots were used in the hacking of Democratic Party leaders.
A search of domain names shows many porn sites are hosted by Webzilla. Some of the domain names on its servers in Holland include the cringe-worthy maturespantyhouse.com, Japanese-toilet.com and asian-pissing-girls.com.
The website o-suck.com is among the domains hosted by Webzilla in Fort Lauderdale. It self describes as “an amazing arousing journey in the land of Endless Lust.”
Porn accounts for about 6 percent XBT’s business, Gurvits said, citing an audit by KPMG. But the count is of subscriber-based porn sites that are hosted by Webzilla —not the much larger universe of pornography moving across file-sharing websites.
Internet porn is generally legal and profitable, and isn’t necessarily a risk to infect computers, cautioned Stephen Cobb, a senior security researcher with ESET North America in San Diego.
“If you are a legitimate supplier of pornography you do not want to mess up your customer’s computers,” he said, distinguishing between sites that sell subscriptions and those that offer porn for free. “People who spend time on the Internet trying to find free porn or trying to watch porn without paying tend to encounter a lot of malicious code.”
And that’s where the file-sharing sites like freakshare.com and 4shared.com, hosted by Webzilla, come into the picture.
The cyber security firm RiskIQ, in a late 2015 report called Digital Bait, estimated that one in three websites that contain pirated content contained malware. That’s software designed to maliciously seek unauthorized computer access to collect private data and/or inflict deliberate harm.
There’s no evidence that XBT and Webzilla actively sought to spread viruses and other malware. But it’s also clear that it has been accused of allowing the kind of pirated porn that is often baited with malware.
“It’s very common for nation states to use that kind of attack,” said a cyber expert with direct knowledge of the hack on Democratic Party leaders.
While claiming to have no knowledge of any Webzilla or XBT role in the attack, the expert said the hack had all the hallmarks of a state actor that hijacked an unsuspecting website to launch an attack. That suggests that clients of Webzilla could have been used without them or host Webzilla being aware of it.
“It’s always some mom-and-pop company some place. Nobody (in intelligence) does it on their own (system),” said the expert, who demanded anonymity given the sensitivity of the matter and ongoing investigations.
Lawsuit Jousting
If the early proceedings are any indication, the XBT lawsuit against BuzzFeed could be a bruising one. The court has ordered each side to hand over confidential data. BuzzFeed has had to give up readership and click data, while XBT must share tax and financial data and, more importantly, details about the internal policing of its hosting operations. No firm trial date has been set yet, and there is still the chance of settlement.
The dossier was in the hands of McClatchy and numerous other news outlets well before it was published by BuzzFeed. And even before then its impact had been felt.
The day after Christmas last year, just weeks before the dossier exploded on the international stage, Gen. Oleg Erovinkin, a former KGB general, was found dead in the back of his car in Moscow.
It wasn’t until a full month later that the world learned this however, when news of his mysterious death became public in news reports from Europe and England on Jan. 27. The reports linked his death to the dossier, which contained certain information that seemed could have only come from him.
Erovinkin was a top aide to Igor Sechin, head of the state energy company Rosneft and widely viewed as the second most powerful man in Russia after Vladimir Putin. Erovinkin was said to have been a go-between for both men
And a day before reports surfaced of Erovinkin’s death, Russian media reported that the top Russian cyber spy, Sergei Mikhailov, was dragged out of an intelligence meeting with a bag over his head and led away in humiliating fashion.
Mikhailov and two others were charged with treason, which led to speculation that they shared information with Steele or a spy agency that gave it to Steele.
Steele has not spoken publicly about the dossier, and did not respond to requests to comment for this story. It may never be known why Steele included the XBT/Webzilla allegations, and proving or disproving them will be extraordinarily difficult, as even those who have complained about the companies acknowledge.
“I have read the dossier. I am familiar with several of the players, as we have spent time investigating them over the years. Mr. Gubarev has taken great care in structuring his enterprises,” said Tucker of Battleship Stance, which also offers content-protection services. “I am not convinced that anyone will find a smoking gun or clear paper trail. It will be near impossible to prove what Mr. Gubarev knew or did not know to the satisfaction of a U.S. court.”
-- Ben Wieder in Washington contributed.
Read more here:
http://www.thenewstribune.com/news/poli ... rylink=cpy